#api-security
Discover more categories and expand your knowledge!allGitHub ActionsCI/CDDevOpsAutomationModular WorkflowsCustom RunnersSelf-Hosted RunnersWorkflow ReusabilityContainerizationAdvanced CI/CDReactAnimationsFramer MotionGSAPWeb DevelopmentUI/UXPerformanceJavaScriptFrontendDeclarative UIAI EngineeringPrompt EngineeringLarge Language ModelsLLM EvaluationMachine LearningMLOpsModel DeploymentGenerative AIAI EthicsData ScienceAPI-FirstOpenAPISwaggerAPI DesignAPI DocumentationREST APIMicroservicesAPI DevelopmentYAMLAPI GatewayAuthenticationRate LimitingTraffic ManagementAPI SecurityAstroIslands ArchitectureWeb PerformanceSSGContent ManagementFrontend DevelopmentVueSvelteAWS LambdaCloudRustAxumWeb APIHigh PerformanceAsynchronousTokioBackend DevelopmentConcurrencyOpenClawAI AgentsMulti-platformWhatsApp APITelegram BotDiscord BotLLM IntegrationConversational AIPythonDeveloper ToolsKotlinEmbabelAutonomous AgentsLLMAgentic AISoftware AgentsAI FrameworksKotlin DevelopmentAI AssistantSpring BootJavaProduction AIRAGAIGPTCode AssistantsIDE PluginsNanobotMCPCustom AgentsPython AutomationDistributed SystemsAgent DevelopmentMulti-TenancySaaS ArchitectureData IsolationCloud ComputingSecurityScalabilityDatabase DesignCloud NativeServerlessProduction ReadyIaCMonitoringReal-TimeWebSocketsServer-Sent EventsSSENode.jsFull-DuplexUnidirectionalAPIPWAOffline-FirstService WorkersCachingIndexedDBResilienceBackground SyncWeb TechnologiesAngularNgRxState ManagementBackendKubernetesContinuous IntegrationContinuous DeploymentDockerSoftware DevelopmentAnti-PatternsCode QualityBest PracticesTechnical DebtRefactoringLegacy CodeSoftware EngineeringMaintainabilityArchitectural DebtClean CodeSoftware ModernizationData EngineeringApache AirflowdbtELTData PipelinesOrchestrationData TransformationSQLDenoDeno 2npmJavaScript RuntimeTypeScriptEnterprise DevelopmentDevSecOpsSecurity AutomationSASTDASTSCAContainer SecurityIaC SecurityPipeline SecurityShift-LeftMulti-Stage BuildsContainer OptimizationDockerfileImage SizeGoReactJsEdge ComputingCloudflare WorkersLow LatencyCDNError HandlingFault ToleranceDeveloper ExperienceDXCLI ToolsCommand Line InterfaceDocumentationTechnical WritingUsabilityUser ExperienceToolingAI DevelopmentJVMOpenAILangChainLangChain4jFrameworksData GovernanceAI SecurityBias MitigationAI ComplianceHuman-in-the-LoopResponsible AIEvent-Driven ArchitectureKafkaDecouplingBiomeToolchainFormatterLinterMultithreadingFearless ConcurrencyOwnershipSynchronizationThreadsMutexChannelsAsync RustCSPContent Security PolicyFrontend SecurityXSSWeb SecuritySecurity Best PracticesHTTP HeadersClient-Side SecurityApplication SecuritySoftware Supply Chain SecuritySLSASigstoreSupply Chain IntegritySoftware ProvenanceCode SigningSBOMOpen Source SecurityArtifact VerificationHTMXHypermediaSPASSRTestingUnit TestingIntegration TestingE2E TestingSoftware QualityTest AutomationModern Software DevelopmentAI in TestingInfrastructure as CodeLLMsConfiguration ManagementScriptingAI/MLCloud AutomationGitGolangGoroutinesParallelismGo ProgrammingGraphQLFederationEnterprise APISupergraphData GraphSchema StitchingRESTgRPCData FetchingProtocol BuffersSystem ArchitectureAWS API GatewayAWS ECRAlpine.jsServer-Side RenderingProgressive EnhancementHTMLModern WebChatGPTAI IntegrationWorkflowsCost OptimizationCloud CostsFinOpsK8sResource ManagementAutoscalingSpot InstancesCloud Financial ManagementAI ToolsProgrammingContext ManagementCoroutinesCSSScroll AnimationsUX/UIAnimationscroll-timelineview-timelineCSS TricksNext.jsClean ArchitectureSoftware ArchitectureDesign PatternsTestabilityDomain-Driven DesignFrontend ArchitectureCLICommand LineClapArgument ParsingRust ProgrammingSystem ToolsRust CratesCSS GridCSS SubgridWeb LayoutsResponsive DesignCSS Best PracticesAdvanced CSSGrid LayoutUI DevelopmentWeb StandardsDatabase ScalingShardingReplicationRead ReplicasHigh AvailabilityDistributed DatabasesPerformance OptimizationSystem DesignSQL DatabasesData ArchitectureConsensusDistributed LockingRedisZooKeeperEtcdCAP TheoremRaftDistributed ComputingContainersProductionFeature FlagsCanary ReleasesDeployment StrategiesA/B TestingProgressive DeliveryContinuous DeliveryGit WorkflowsMerge QueuesStacked Pull RequestsVersion ControlCollaborationGit Best PracticesGitOpsArgo CDFlux CDDeclarative InfrastructureReliabilityIdiomatic GoPatternsDevelopmentRobustnessIntersectionObserverLazy LoadingUX OptimizationBrowser APIScroll EventsOptimizationAI TestingNatural Language ProcessingEvaluation MetricsDevOps AISoftware TestingLocal-FirstOPFSOffline AppsProgressive Web AppsClient-Side StorageWeb APIsData PersistenceContainer QueriesFlexboxFront-endLayoutComponent-drivenModern CSSMulti-CloudTerraformOpenTofuAWSAzureGCPCloud StrategyApp RouterStreamingServer ActionsFull-stackNative Test RunnerJest AlternativeTDDAssertionPostgreSQLDatabaseIndexingQuery OptimizationPerformance TuningDBAExplain AnalyzeVacuumPartitioningAPI IntegrationDeveloper GuideAI Best PracticesRetrieval-Augmented GenerationVector StoreNLPProfilingBenchmarkingSystems ProgrammingZero-Cost AbstractionsCode TuningHigh Performance ComputingBorrowingMemory SafetyLifetimesBorrow CheckerRust LangRxJSSLMFine-tuningLocal AIEdge AIQuantizationPEFTLoRAHugging FaceOn-device AISpatial ComputingVisionOSXR DevelopmentAugmented RealityVirtual RealitySwiftUIRealityKitReality Composer ProImmersive ExperiencesSvelte 5RunesReactivityFrontend PerformanceJavaScript FrameworksCompilerSvelteKitTailwind CSSTailwind v4CSS FrameworkUtility-First CSSMigration GuideFront-end DevelopmentPostCSSJIT CompilerStylingEvent LoopAsynchronous JavaScriptPromisesasync/awaitLibuvNon-blocking I/OView Transitions APIUX AnimationMPAUI DesignAdvanced TypeScriptLarge Scale AppsType GuardsConditional TypesMapped TypesDeclaration MergingGenericsMonorepoCore Web VitalsLCPINPCLSHydrationStreaming SSRArchitectureMonolithicC++MigrationFFIMavenGradleXMLCSS ArchitectureStyled ComponentsCSS ModulesComponent-Based StylingCSS-in-JSScalable CSSNxTurborepoBazelBuild SystemMCP AgentLightweight AgentIoTEmbedded SystemsRemote ManagementC2FrameworkRoboticsMulti-Agent SystemsReinforcement LearningNext.js 15React 19React CompilerFull-Stack FrameworkStatic Site GenerationObservabilityOpenTelemetryDistributed TracingMetricsLoggingSREApplication MonitoringTracingAgent HardeningProduction ReadinessMachine Learning SecurityThreat ModelingAccess ControlData PrivacyPlatform EngineeringInternal Developer PlatformIDPSelf-ServicePost-Quantum CryptographyPQCQuantum ComputingCybersecurityNISTCryptographic AgilityHybrid CryptographyTLSDigital SignaturesKey ExchangePulumiPyScriptPyodideWebAssemblyWasmBrowser PythonInteractive WebLong-ContextVector DatabasesAI ArchitectureKnowledge RetrievalContext WindowMemoizationBuild ToolsServer ComponentsRSCFullstackZustandJotaiSignalsWebRTCCRDTsMultiplayerPeer-to-peerConflict ResolutionMicrocontrollersRTICHALNo-stdBare-metalSafety-criticalProgramming LanguageEcosystemFuture TechUndefined BehaviorSystem Programmingwasm-bindgenweb_sysMicro-FrontendsModule FederationEnterprise ArchitectureComponent-BasedAnthropicKotlin AIREST APIsAuthorizationSelf-Healing InfrastructureAIOpsIncident ManagementProduction MonitoringSite Reliability EngineeringPredictive AnalyticsAnomaly DetectionServer-Driven UISDUIMobile DevelopmentCross-PlatformDynamic UIJSON SchemaServerless 2.0Stateful ApplicationsFaaSBaaSDurable ObjectsJenkisRedux toolkitOperationsCUEDaggerConfiguration as CodePipelineDeclarativeType SafetySupabaseFirebase AlternativeBackend as a ServiceOpen SourceRealtimeEdge FunctionsRow Level SecurityFull Stack DevelopmentOpen-source AIDeep LearningQLoRADatabasesTursoNeonXataSQLiteData ManagementPandaCSSVanillaExtractFrontendDevelopmentDesignSystemsZeroRuntimeCSSAtomicCSSWebPerformancePlaywrightWeb TestingFrontend TestingQuality AssuranceAgentic UIAI-Driven UIUser Interface DesignFrontend AIHuman-Computer InteractionBunRuntimePackage ManagerBundlerWasmEdgeSpinWASIGin FrameworkReactive ProgrammingSoftware DesignSOLID PrinciplesGeminiAutonomous AIAgentic WorkflowTool UseMemory ManagementSelf-Hosted AIPrivacyDeploymenteBPFNetworkingLinux KernelCiliumFalcoWeb Speech APISpeech RecognitionSpeech SynthesisAccessibilityVoice UIQUICHTTP/3Network PerformanceWeb ProtocolsTLS 1.3UDPHTTPLatencyInternet ProtocolsPostgrespgvectorVector SearchEmbeddingsSimilarity SearchAWS S3Vector DatabasePineconeWeaviateData StorageWeb Accessibilitya11yWCAGSemantic HTMLARIAKeyboard NavigationInclusive DesignAccessibility TestingWeb ContainersBrowser DevelopmentClient-Side ScriptingInteractive DevelopmentWeb3dAppsBlockchainDecentralizationSmart ContractsEthereumSolidityIPFSDAODeFiGameFiLayer 2Zero-Knowledge ProofsZKPCryptographyDecentralized Identityzk-SNARKsZero TrustIAMNetwork Security
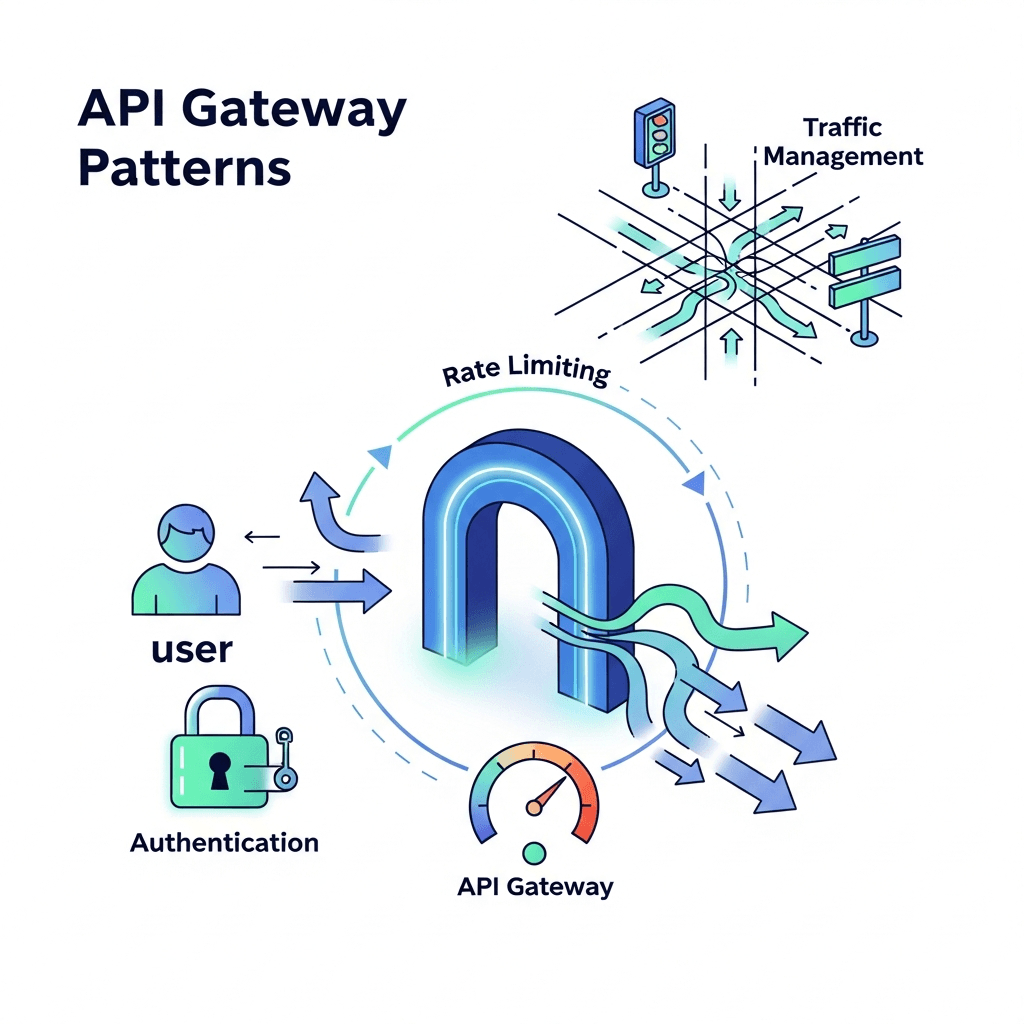
API Gateway
API Gateway Patterns: Authentication, Rate Limiting, and Traffic Management Demystified
March 02, 2026•15 min read
REST APIs
Securing REST APIs: Authentication, Authorization, Best Practices
January 27, 2026•2 min read
Zero Trust